ISO 27001 management software
Prepare your organization for ISO 27001 certification
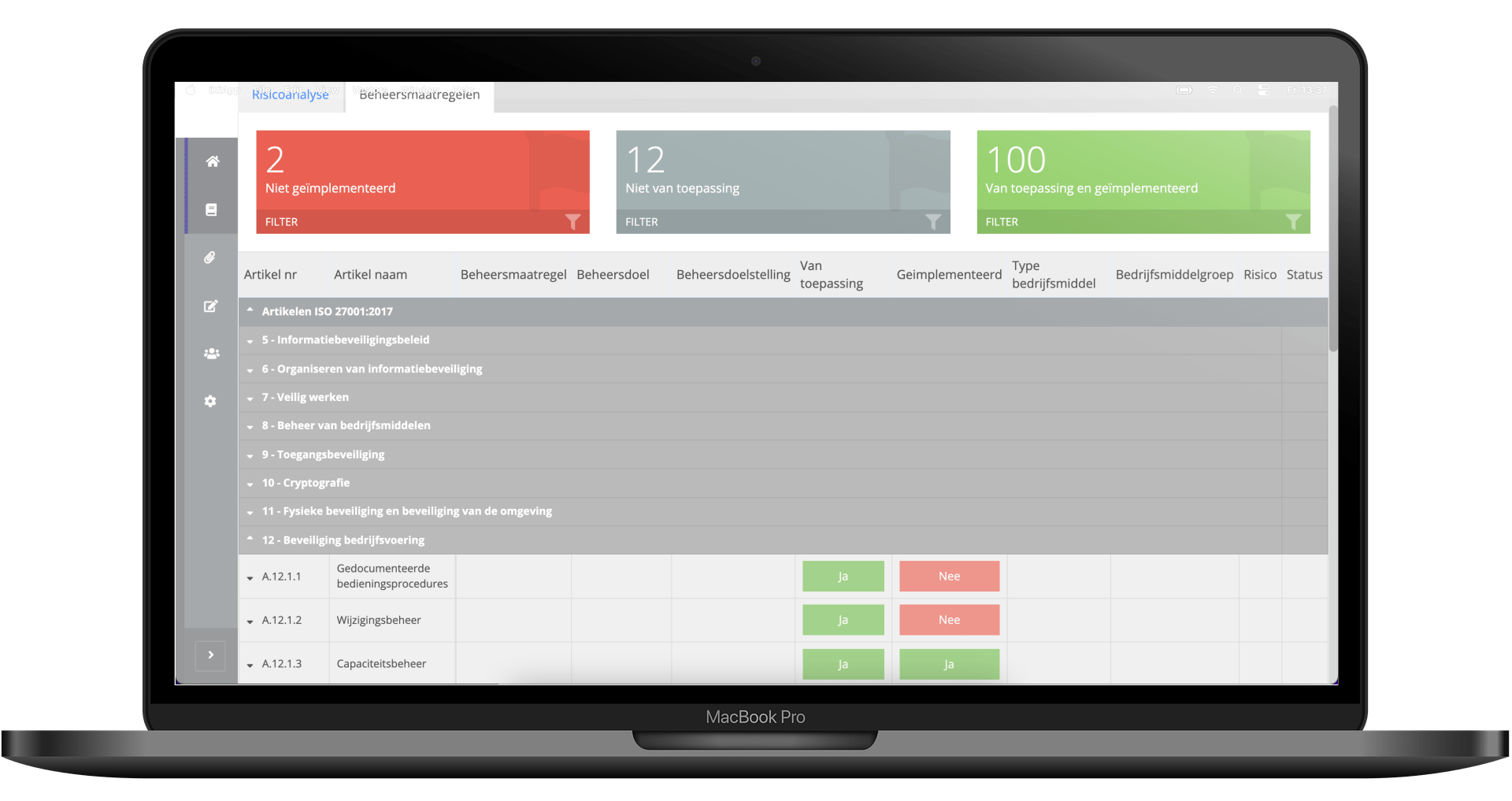
Software tool for information security guidelines
Would you like to prepare your organization for ISO 27001 certification? This can easily be done with the PCT (ProActive Compliance Tool). This software tool provides you with tools to meet the requirements of the ISO standard with regard to information security in a structured and clear way.
The software compliance tool is there to go through the process with you based on your company information. And to indicate which legal and regulatory requirements you must meet as an organization. The PCT ensures that you can go through the steps of this process in an unambiguous way to ensure that the audit runs smoothly.

What is the ISO 27001 standard for information security?
The international standard ISO 27001 for information security standard is there to demonstrate that your organization handles information in a responsible and confidential manner and ensures that adequate security measures are implemented. After all, as a company you should not think that information, such as personal data of customers, falls into the wrong hands. The standard specifies requirements for establishing, implementing, executing, checking, assessing, maintaining and improving a documented Information Security Management System (ISMS) in the context of the general business risks for your organization. By implementing an ISMS you guarantee the availability, integrity and confidentiality of information within the organization.
By working with the ISMS and thereby complying with the standard, you as an organization show that all risks associated with confidential handling of information are managed correctly.
The ISO 27001 compliance checklist
Make sure your organization is well prepared for the audit for the certification of the information security management system with our ISO 27001 checklist.
Based the checklist, we will go through the necessary documents that are part of the Information Security Management System, abbreviated ISMS. We will go through the ISO 27001 checklist on the basis of 5 steps and will give a number of examples.
“The PCT is a tool that helps you step by step and prepares your organization for the process towards certification in accordance with ISO 27001.”
GDPR in relation to ISO 27001
The General Data Protection Regulation (GDPR) is a European law that was created to guarantee the protection of personal data within the EU. All organizations in the Netherlands and within the European Union must comply with this. The GDPR requires that personal data is protected with appropriate technical and organizational measures. Many subjects in the GDPR can be secured in an ISMS based on ISO 27001. Complying with the ISO 27001 standard helps you as an organization to implement measures for appropriate protection of personal data and, possibly in combination with ISO 27701, to demonstrably comply with the GDPR.
The ISO 27001 audit
An audit-based certification process can be one that you have never experienced before. There can be many ambiguities, which can lead to stress. That is why it is nice if there is a tool that can guide you to ensure that the audit, which must lead to certification, for ISO 27001 and/or other standards runs smoothly for your organization. The PCT is a tool that takes you step-by-step and prepares your organization for the process towards certification in accordance with ISO 27001. An independent certification body (CB) will assess whether your organization meets the certification criteria for the ISO 27001 standard. Any shortcomings will be fed back by the CB if the processes still need to be improved. With a positive result of the audit, the certification follows and you receive the official ISO 27001 certificate!
What do our customers say?
Who better than our customers, can tell you what they think of the PCT.
Benefits of an ISMS conform ISO 27001 in the PCT
Helps your organization demonstrably comply with the relevant laws and regulations
Risks and measures of your organization are controlled
Process of planning and control is secured with recurring tasks
Policies and processes (including information security) are well established and safeguarded
Provides support in working according to fixed structure
Provides confidence and assurance to customers regarding handling of information
A software tool suitable for all standards
The PCT is suitable for all common standards, certification schemes and assessment guidelines. Read more about ISO certification.